Frequently Asked Questions
CLICK Here to see screenshots on how to configure several SIP endpoint brands
None, NATPass™ is optimized for best performance therefore almost all logic needed is built-in. In fact, it is best not having “by default” services like Apache, php, mysql, xinetd running in the server. In some cases DNS cache service is recommended but not required. NATPass™ can be integrated with Linux firewall, in that case IP Tables needs to be installed as well. Few Linux core libraries are also used.
It is a matter of downloading the missing libraries for the distribution used, usually available on line. Many customers run NATPass™ on pretty much any Linux distribution. Please download the installation guide that include details on how to install missing libraries.
NATPass™ is build for Linux only and can run in most linux distributions. The preferred distributions today are Centos, Fedora, Ubuntu and Red-hat.
That is part of the unique algorithm from NATPass™. It basically discovers what kind of NAT it is dealing with for each call and makes use of SIP signaling options (183 session progress; re-invite) to redirect media stream to pinhole opened by current session in remote firewalls.
No. It uses some SIP specific features to traverse through NAT/Firewall and only your SIP PHONE can use it. It does not compromise your network.
Natpass is licensed according to number of registered devices. The number of channels or concurrent calls from those registered devices is not limited. Licenses are generated based on the IP address of the server running the application. If the IP address is changed the apllication would become unlicensed, to avoid that, a new license would have to be issued (processing fee might apply).
No. It supports only UDP. But TCP support is on the roadmap.
NATPass™ binds with only one network interface and one IP address. However you have the option of configuring a second interface/IP address that is used by the application to discover more efficiently what kind of NAT is the remote SIP device connecting from.
Yes, NATPass™ does not require one of the endpoints on a public IP address. RTP or media stream will flow directly between endpoints in almost all cases except when one of the devices is behind a symmetric NAT (see question about symmetric NAT)
No. It supports only SIP. Outdated or proprietary protocols are not supported.
Any SIP compliant (rfc 3261) device should work fine. They must support Outbound Proxy. Refer to NATPass™ web site for a list of Interop tested manufacturers.
Yes and Yes, NATPass™ is a software solution however our partners can provide pre-loaded 2U or 4U servers.
It should work with any type of firewall including Symmetric NAT. Symmetric NAT is performed only by advanced enterprise routers, in that case NATPass™ will recognize this scenario and will make the call succeed by signaling and doing RTP bridging. It is all transparent for the user and there is no need to reconfigure anything.
You can find classification of NAT in RFC 3489 – STUN
http://www.faqs.org/rfcs/rfc3489.html.
However you don't have to worry about that, with NATPass™, it does not mater what type of firewall or NAT you have.
NATPass™ and any other VoIP SBC or nat traversal solution can’t traverse advanced firewalls where explicit rules for blocking VoIP ports/service have been configured. This is unlikely to happen for residential/SOHO users and most enterprises.
They are two different solutions. STUN is less universal. NATPass™ works in many more situations where STUN alone does not work. STUN will not work if you are working behind new symmetric NAT routers. You can use STUN if you are familiar with configuring SIP devices to work behind NA, If your PHONE supports STUN, and if your NAT is not Symmetric. Many times you would need to configure the Remote firewall with some port forward rules. STUN can be problematic when there is multiple IP phones behind the router, some extreme cases require forcing IP phone's source port to be unique in same LAN.
Yes, Video calls work. And in many cases all media stream is released however there are some not mature video phone implementations that might require some modification in order to having NATPass™ releasing video media stream. Anyhow, video calls work and media will be automatically bridged by NATPass only when needed.
The ports used are configurable. You can use a less known port to hide your application and reduce network scan hits. For SIP signaling it uses 5 ports: the base port configured and the four consecutive ports. All devices should be configured to connect to the base port. Regarding media ports or RTP ports, the range is configured, the number of ports in the range must be at least twice the number of concurrent calls you plan to have.
Yes, Media relay is called Full Mode and can be configure per domain or per SIP extension. You can have some customer in Full Mode and others with Media relay or Media Path Optimization.
Yes and Yes, you can achieve redundancy by using DNS SRV records. Also in NATPass™ you can configure redundant entries for your IPPBX or Registrar/SIP server. It can be used for failover or load balancing.
You can either fill out our contact form and specify your question there or contact us by email or phone. Click here to see our contact page
CLICK here to see a detailed explanation on NATPass DoS/DDoS protection
i.e there are two SIP servers sitting on different physical servers in the network. Wnat NAT PASS to send say 50 % calls to server A and 50 % calls to Server B.
In the natpass.cfg file you add the modifier SRV to the domain. Endpoints should register to a domain.
SRV Modifier will make Natpass look inside the config file for server entry to resolve where to forward those requests in that case DNS is not used for that domain for Invite and Register requests.
The settings below is an example in which natpass will load balance traffic for endpoints registering to xxx.testing.conm between .5 and .6 For yyy.testing.com it will always send to .5
domain = xxx.testing.com SRV
domain = yyy.testing.com SRV
server = xxx.testing.com 50 192.168.201.5:5060
server = xxx.testing.com 50 192.168.201.6:5060
server = yyy.testing.com 100 192.168.201.5:5060
*Disclaimer: The listed Interop Tested Products have been tested by NATPass™. However, we cannot certify that all models will work in each environment. It may depend on different versions, models, and network design. Products should be checked for every environment.
How to find out current registered contacts or phones
There is built in scripts that can be run from linux console.
#cd /usr/local/natpass/bin
#./count.sh
#cat count.log
The output is a list of all contacts and a summary of current registered devices and active sessions.
Please notice that If your natpass.log file is too large (more than 1 GB) and depending on traffic and memory size on your server this command might not execute.
How do I restart Natpass and verify the Natpass code version and license size?
Natpass should be configured to autostart with the server however if there is need to stop/start the service manually the following commands can be used thru Linux console: ( the # is the linux console prompt) # /usr/local/natpass/bin/natpass_ctl stop # /usr/local/natpass/bin/natpass_ctl start
After restarting Natpass the license size can be verified with the following command: # grep "users version" /usr/local/natpass/logs/natpass.log
An example output for a 500 endpoints license is: 500-users version.
After restarting Natpass the license size can be verified with the following command: # grep "Build" /usr/local/natpass/logs/natpass.log
An example of code version is: Build 19.04.30
Introduced in version 3.6
This is how you configure if Natpass is on a Private IP.
If your natpass is on a private IP, first make sure SIP and RTP ports are forwarded to NATPASS internal IP.
In the configuration file natpass.cfg:
Define the external public IP. This IP is used to license Natpass and needs to be mapped to server internal IP. ipaddr = xxx.xxx.xxx.xxx
Define the internal IP on the server. Natpass will bind to private_ipaddr = yyy.yyy.yyy.yyy
There is also an optional parameter to configure if all your PBXs/SIP Registrar servers are in same segment/subnet as natpass or reachable (without NAT) using internal natpass IP.
Define the Natpass IP to be used to reach the PBX (same value a private_ipaddr) server_ipaddr = yyy.yyy.yyy.yyy
If your PBXs/SIP Registrar servers are reachable thru public IP, do not specify this parameter: server_ipaddr .
This is how you configure if Natpass is directly running a public IP.
In the configuration file natpass.cfg:
Define server's public IP. This IP is used to license Natpass.
ipaddr = xxx.xxx.xxx.xxx
Make sure to Comment out or remove the following parameters
#private_ipaddr = yyy.yyy.yyy.yyy
#server_ipaddr = yyy.yyy.yyy.yyy
Version 3.7 introduced a new feature called Quiet Mode.
This setting is designed to make the task of network scanners harder. By default NatPass responds to all SIP requests (when sender is not in black DDOS list). Scanners will send rogue SIP packets and if found response they know there is a live SIP server there which prompts more attempts and brute force attacks.
When quiet_mode = yes Natpass does not respond and quietly drop rogue SIP requests sent with any domain not defined in the configuration file.
New version 3.7 includes a new setting for the configuration file to correct this.
Some PBX vendors use CSTA encapsulated in SIP messages to signal status change like DND between phone and PBX.
A SIP endpoint can lose network suddenly. By default natpass checks for RTP in all INVITE dialogs in case a client stops sending RTPs with out proper call disconnection signaling so it can disconnect the call.
This causes a problem because natpass would close the dialong carrying CSTA updates in which is normal that no RTP is transmitted.
If you have this scenario add the following to the configuration file:
check_rtp_flow = false
Can I restrict Natpass to work with specific SIP Domains and device SIP User Agent
Domain should be defined with the keyword 'RSTS':
i.e
domain = *.mymsp.com RSTR FULL PRSN
domain = pbxn.othermsp.com RSTR FULL PRSN
For those domains, Natpass will only allow connections from SIP client that present the correct User Agent headers (User-Agent:) definedin the "broken" section with Y modifier.
Y means Yes pass traffic for this User-Agent even if is for a restricted domain.
i.e
broken = Y Cisco
broken = Y Yealink
broken = YAIsT Polycom
broken = YE Grandstream
broken = YD Grandstream HT-5
broken = Y Fanvil
Matching of UserAgent: Max length first.
For example by specifying those two lines you can prohibit one particular "Telco" User-Agent and allow all other:
broken = Y Telco
broken = - Telco Systems AC-211
Yes, Natpass As A service is offered thru ABPTech ( www.abptech.com).
You can start right away and just pay for your monthly usage based on the number of devices you are running thru Natpass AAS platform.
The PBX vendor has made the SBC field not configurable with any URL as it was before version 18 Update 5. Only allows pre-defined internal on-premise SBCs.
How can I continue to use Natpass AAS Cloud SBC ?
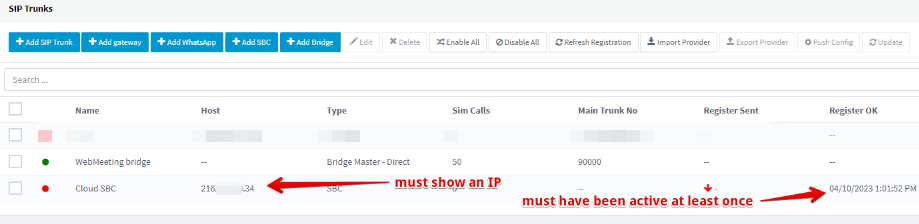
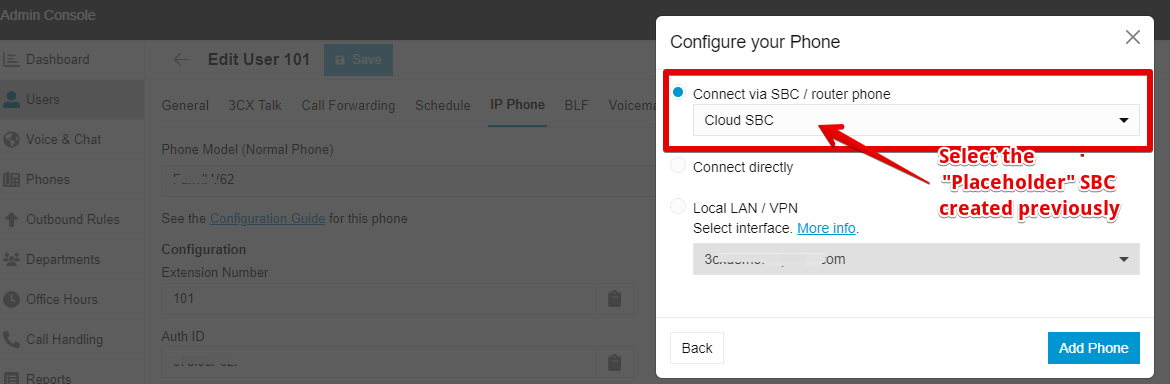
1. Create a "Placeholder" SBC in 3CX console.
Under SIP Trunks, Click on "ADD SBC". Give it a name (i.e. CloudSBC).
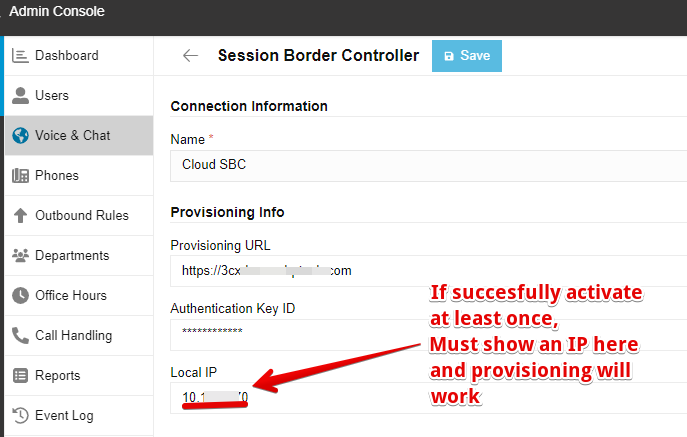
In version 18 update 7 that "placeholder" SBC in 3CX console had to be active at least once. If that is not the case provisioning fails.
Windows 3cxSBC can be easily installed/uninstalled for this task. You can then repurpose/disconnect/uninstall the SBC but do not remove it from the PBX configuration. Phones will provision and work as usual with Natpass.
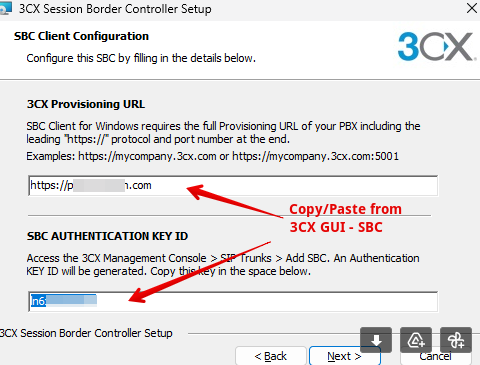
Few seconds after finishing installing, it should show as active in 3CX GUI. After that you can uninstall the 3CX sbc as is not needed anymore.
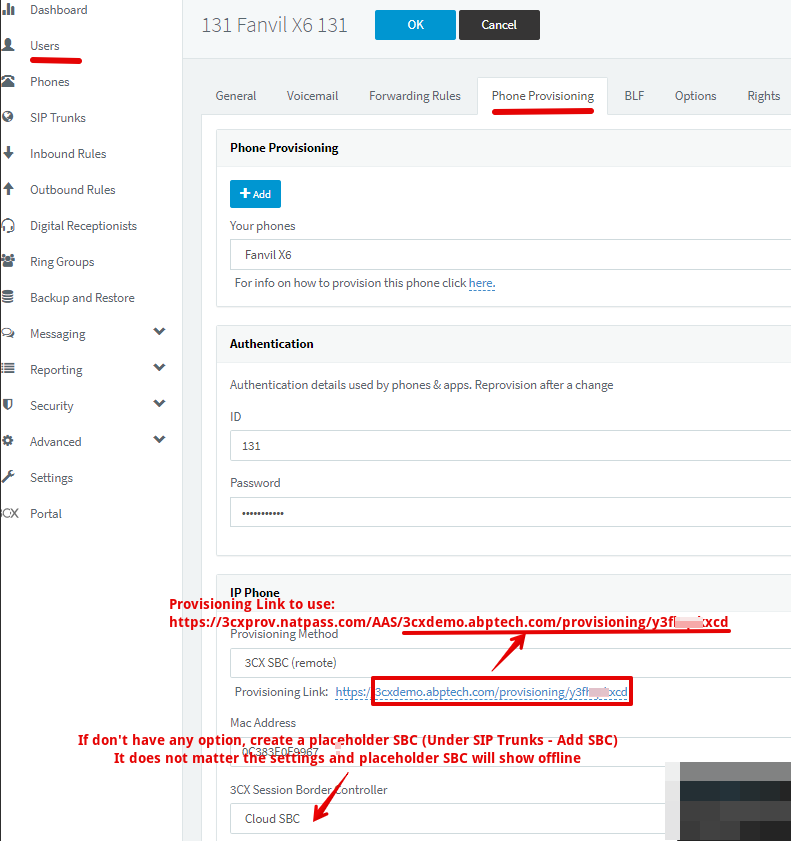
2. Provision the phones using the provisioning URL as explained below
All you need to do is changing the Configuration/Provisioning server URL in the phone, this is done using ZTP or phone GUI.
Prepend "3cxprov.natpass.com/<NatpassServerID>" to the provisioning server URL value. This is how new value should look like:
https://3cxprov.natpass.com/<NatpassServerID>/<3CXServer/path address>
Replace:
- <NatpassServerID> If you use Natpass As A Service use "AAS". If you have your own Natpass server address please request your NatpassServerID by emailing info@natpass.com .
- <3CXerver/path address> with your own 3CX Provisioning URL
Notice the https:// is only at the beginning of the URL.
For example:
Original Provisioning link: https://example1.my3cx.us/provisioning/ulhck4c4w5yvujt
Provisioning link to use: https://3cxprov.natpass.com/AAS/example1.my3cx.us/provisioning/ulhck4c4w5yvujt
Below an example showing 3CX console:
For all this to work, We have made available a provisioning translation service free of charge for all Natpass owners with valid/current maintenance or Natpass As A Service (AAS) users. This translation service maintains intact and keeps in sync all settings for the phones as provisioned from PBX but changes the SBC address so the phone is directed to Natpass server.
As an additional benefit the translation service will also provision a seconday/redundant Natpass AAS SBC address in the phones (Yealink or Fanvil) providing a even more resilient SIP connectivity for your phones.
It is also worth mentioning that this provisioning translation service is running in a highly available and secure serverless cloud infrastructure. Other than operation logs, this service does not store any data.
How to Configure Snom Phones to use Cloud SBC
For Snom phones we have to create a custom template.
Unofrtunatelly custom templates are not supported in 3CX hosted versions.
Download the template you'll be using from here (Use Save Link As to download as file): snom_sbc_aas Template
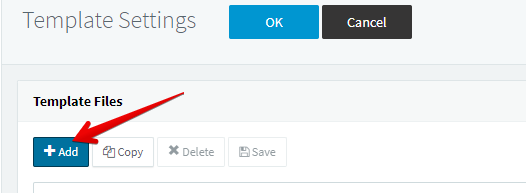
Under Settings look for the Templates tile.
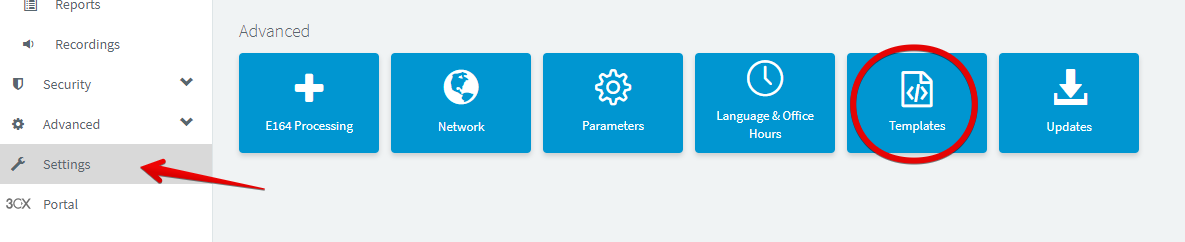
Add a new template and give it a proper name
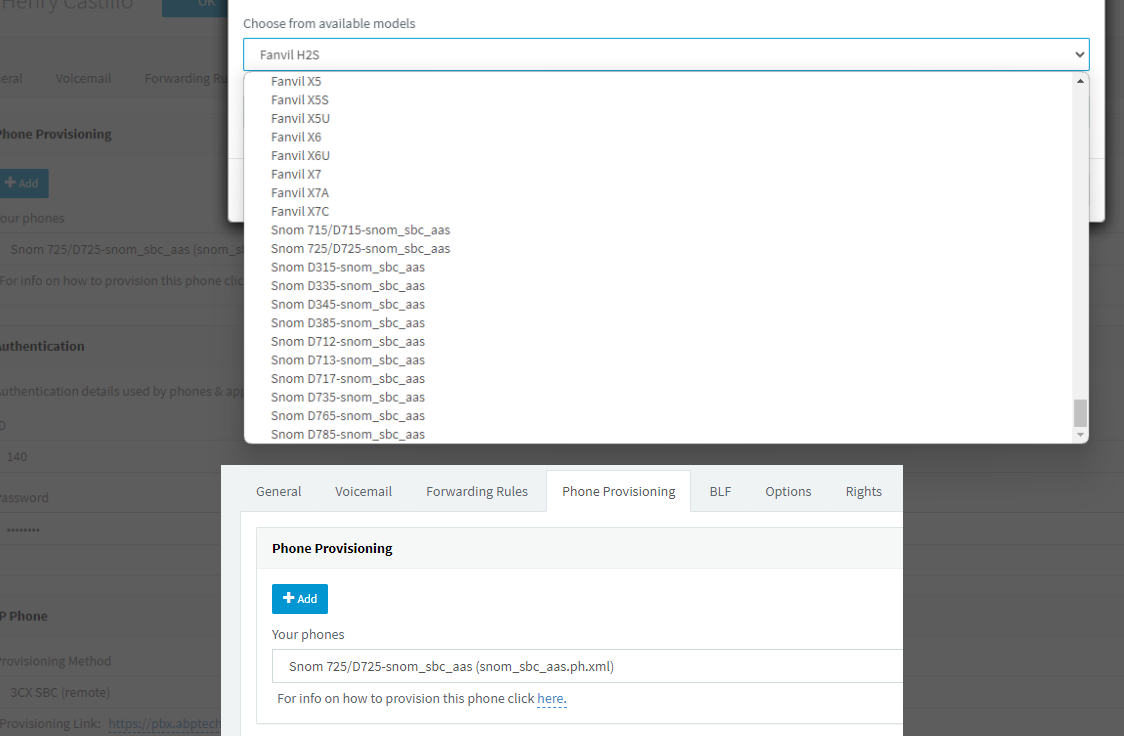
When configuring an extension scroll all the way down to find your custom templates.
Provision the phone as normal
When phones do not provision for 3CX:
1. Make sure you followed the instructions in this FAQ
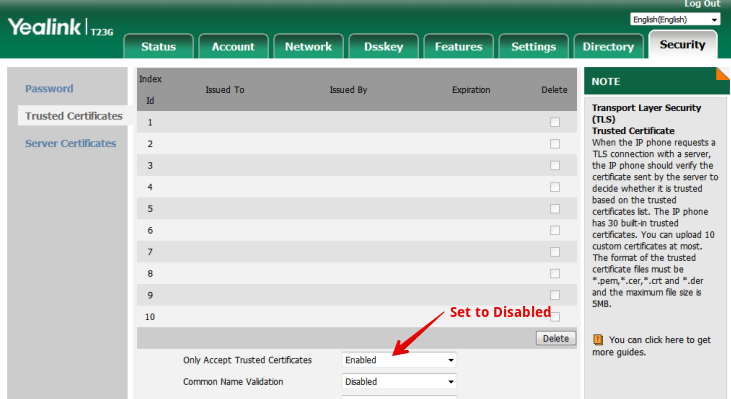
2. If the above fails, you might be using an older phone/firmware. Some of those do not have https certificates loaded thus you need to load the 3CX recommended firmware for the model and/or change a setting in the phone to accept all https certificates:
How can I continue to use Natpass AAS Cloud SBC ?
No different from V18.
1. Create a "Placeholder" and Register once an SBC in 3CX console.
Open Admin console and Under "Voice & Chat", Click on "ADD SBC". Give it a name (i.e. CloudSBC).
In version 20 that "Placeholder" SBC in 3CX console had to be active at least once. If that is not the case provisioning fails.
For this purpose, Windows 3cx SBC can be easily installed/uninstalled for this task. You can then repurpose/disconnect/uninstall the SBC but do not remove it from the PBX configuration. Phones will provision and work as usual with Natpass.
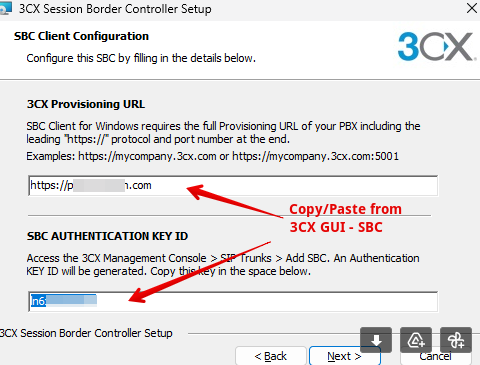
Few seconds after finishing installing, the "Placeholder" 3CX SBC should show as active in 3CX GUI. After that you can uninstall the 3CX sbc as is not needed anymore.
2. Provision the phones using the provisioning URL as explained below
All you need to do is changing the Configuration/Provisioning server URL in the phone, this is done using ZTP or phone GUI.
Prepend "3cxprov.natpass.com/<NatpassServerID>" to the provisioning server URL value. This is how new value should look like:
https://3cxprov.natpass.com/<NatpassServerID>/<3CXServer/path address>
Replace:
- <NatpassServerID> If you use Natpass As A Service use "AAS". If you have your own Natpass server address please request your NatpassServerID by emailing info@natpass.com .
- <3CXerver/path address> with your own 3CX Provisioning URL
Notice the https:// is only at the beginning of the URL.
For example:
Original Provisioning link: https://example1.my3cx.us/provisioning/ulhck4c4w5yvujt
Provisioning link to use: https://3cxprov.natpass.com/AAS/example1.my3cx.us/provisioning/ulhck4c4w5yvujt
Below an example showing 3CX console:
For all this to work, We have made available a provisioning translation service free of charge for all Natpass owners with valid/current maintenance or Natpass As A Service (AAS) users. This translation service maintains intact and keeps in sync all settings for the phones as provisioned from PBX but changes the SBC address so the phone is directed to Natpass server.
As an additional benefit the translation service will also provision a seconday/redundant Natpass AAS SBC address in the phones (Yealink or Fanvil) providing a even more resilient SIP connectivity for your phones.
It is also worth mentioning that this provisioning translation service is running in a highly available and secure serverless cloud infrastructure. Other than operation logs, this service does not store any data.
IMPORTANT NOTES:
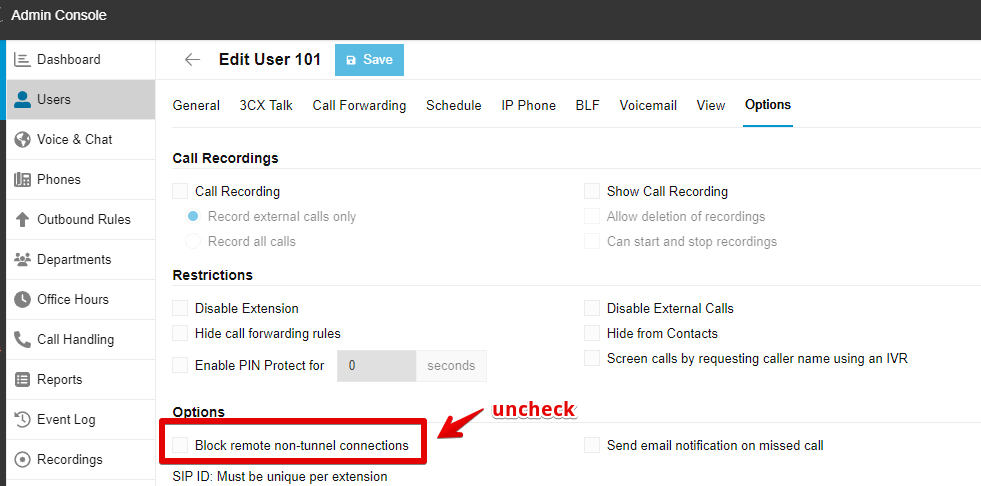
When using Natpass the remote phones connect to the PBX (thru Natpass) using SIP. For that reason, make sure to unckeck "Block remote non-tunnel connections" (for 3cx version 18 uncheck "Block remote phones using stun") under Options settings for that extension/user.
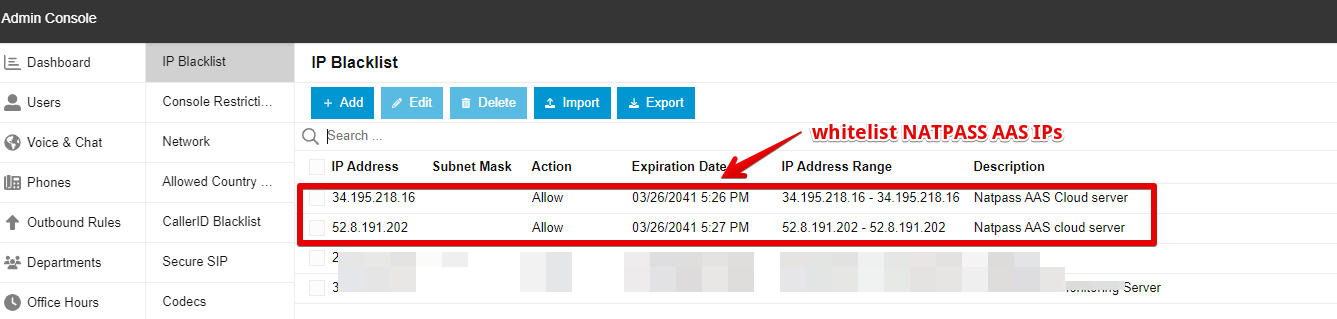
To avoid your 3CX server incorrectly blacklisting natpass cloud servers add the following natpass server IPs to your 3CX server whitelist: 34.195.218.16 and 52.8.191.202
3CX version 20 introduced an interoperability issue with previous Natpass versions and has been fixed in the latest release 3.8.6
If you have a permanent license with maintenance up to day, download the new rpm and install it in your server.
rpm -Uvh natpass-3.8-8.el7.x86_64.rpm
In addition to installing version 3.8.6 or later you need to add the following 3 lines to Natpass config file (natpasss.cfg) to fix the Call Park/Pickup issue:
#
broken = v 3CXPhoneSystem 2
#
Natpass AAS users don't need to to anything as the AAS server's cluster has been updated.
